Overview
What is CyberArk Privileged Access Management?
CyberArk is a privileged account and access security suite issued by the company of the same name in Massachusetts . The Core Privileged Access Security Solution unifies Enterprise Password Vault, Privileged Session Manager and Privileged Threat Analytics to protect an…
Product Details
- About
- Integrations
- Competitors
- Tech Details
- Downloadables
- FAQs
What is CyberArk Privileged Access Management?
CyberArk offers Identity Securitycentered on
privileged access management. CyberArk provides a security offering for any
identity – human or machine – across business applications, distributed
workforces, hybrid cloud workloads and throughout the DevOps lifecycle, and
their solutions are used to secure all identities and critical assets.
CyberArk PAM solutions protect sensitive access across on-premises, cloud, and hybrid infrastructures. Designed from the ground up for security, PAM solutions help organizations by measurably reducing cyber-risk. This is accomplished by managing privileged account credentials and access rights, proactively isolating and monitoring privileged account activity, and quickly responding to threats. CyberArk PAM solutions can work with CyberArk Identity Single Sign-On and Multifactor Authentication tools, to securely access to on-premises, cloud, mobile and legacy apps. CyberArk PAM also works with third party MFA and SSO solutions as well.
Customers have 350+ OOTB software integrations available in the CyberArk Marketplace, with over 235 technology vendors, ranging from security technologies, cloud service providers, IoT, OT, and web applications.
CyberArk Privileged Access Management Features
- Supported: Manage Privileged Credentials
- Supported: Isolate & Monitor Sessions
- Supported: Threat Detection & Response
- Supported: Manage Nomadic Devices
- Supported: Remote Access to PAM
- Supported: Adaptive MFA & SSO
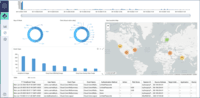
CyberArk Privileged Access Management Screenshots
CyberArk Privileged Access Management Videos
CyberArk Privileged Access Management Integrations
- Cisco Routers
- Fortinet FortiGate
- Cisco Identity Services Engine (ISE)
- Veritas NetBackup Appliance
- AlgoSec
- AWS
- Azure
- GCP
- SailPoint
- Okta
- ServiceNow
- Splunk
- CrowdStrike
- VMware
- Citrix
- Palo Alto
- Sphere Privileged Monitoring
- Fireeye
- Backbox
- Red Hat
CyberArk Privileged Access Management Competitors
CyberArk Privileged Access Management Technical Details
| Deployment Types | On-premise, Software as a Service (SaaS), Cloud, or Web-Based |
|---|---|
| Operating Systems | Windows, Linux |
| Mobile Application | Apple iOS, Android, Mobile Web |
| Supported Countries | Americas, Israel, UK, Canada, France, GMBH, Spain, Netherlands, Italia (Milan), Italia (Rome), Turkey, Australia, Asia Pacific, Japan, India, Denmark |
| Supported Languages | Arabic, German, English, Spanish, French, Italian, Japanese, Korean, Dutch, Portuguese, Brazil Portuguese, Russian, Serbian, Swedish, Thai, Vietnamese, Chinese, Simplified Chinese - Traditional |