Microsoft Defender for EndpointFormerly Microsoft Defender ATP
Overview
What is Microsoft Defender for Endpoint?
Microsoft Defender for Endpoint (formerly Microsoft Defender ATP) is a holistic, cloud delivered endpoint security solution that includes risk-based vulnerability management and assessment, attack surface reduction, behavioral based and cloud-powered next generation protection, endpoint detection and response (EDR), automatic investigation…
How Microsoft Defender for Endpoint Differs From Its Competitors
Awards
Products that are considered exceptional by their customers based on a variety of criteria win TrustRadius awards. Learn more about the types of TrustRadius awards to make the best purchase decision. More about TrustRadius Awards
Popular Features
- Malware Detection (53)8.585%
- Infection Remediation (52)8.282%
- Anti-Exploit Technology (51)8.080%
- Centralized Management (52)7.979%
Reviewer Pros & Cons
Pricing
Academic
$2.50
Standalone
$5.20
Entry-level set up fee?
- No setup fee
Offerings
- Free Trial
- Free/Freemium Version
- Premium Consulting/Integration Services
Product Demos
Microsoft Defender for Endpoint Overview
Features
Product Details
- About
- Competitors
- Tech Details
- FAQs
What is Microsoft Defender for Endpoint?
Rapidly
stops threats: Protects against sophisticated threats such as
ransomware and nation-state attacks.
Scales security: Puts time back in the hands of defenders to prioritize risks and elevate the organization's security posture.
Evolves the organization's defenses: Goes beyond endpoint silos and mature the organization's security based on a foundation for extended detection and response (XDR) and Zero Trust.
Microsoft Defender for Endpoint Features
Endpoint Security Features
- Supported: Anti-Exploit Technology
- Supported: Endpoint Detection and Response (EDR)
- Supported: Centralized Management
- Supported: Infection Remediation
- Supported: Vulnerability Management
- Supported: Malware Detection
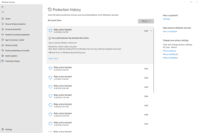
Microsoft Defender for Endpoint Screenshots
Microsoft Defender for Endpoint Video
Microsoft Defender for Endpoint Competitors
Microsoft Defender for Endpoint Technical Details
| Deployment Types | On-premise |
|---|---|
| Operating Systems | Windows |
| Mobile Application | No |