Excellent choice for you business Secrets Management Solution
Use Cases and Deployment Scope
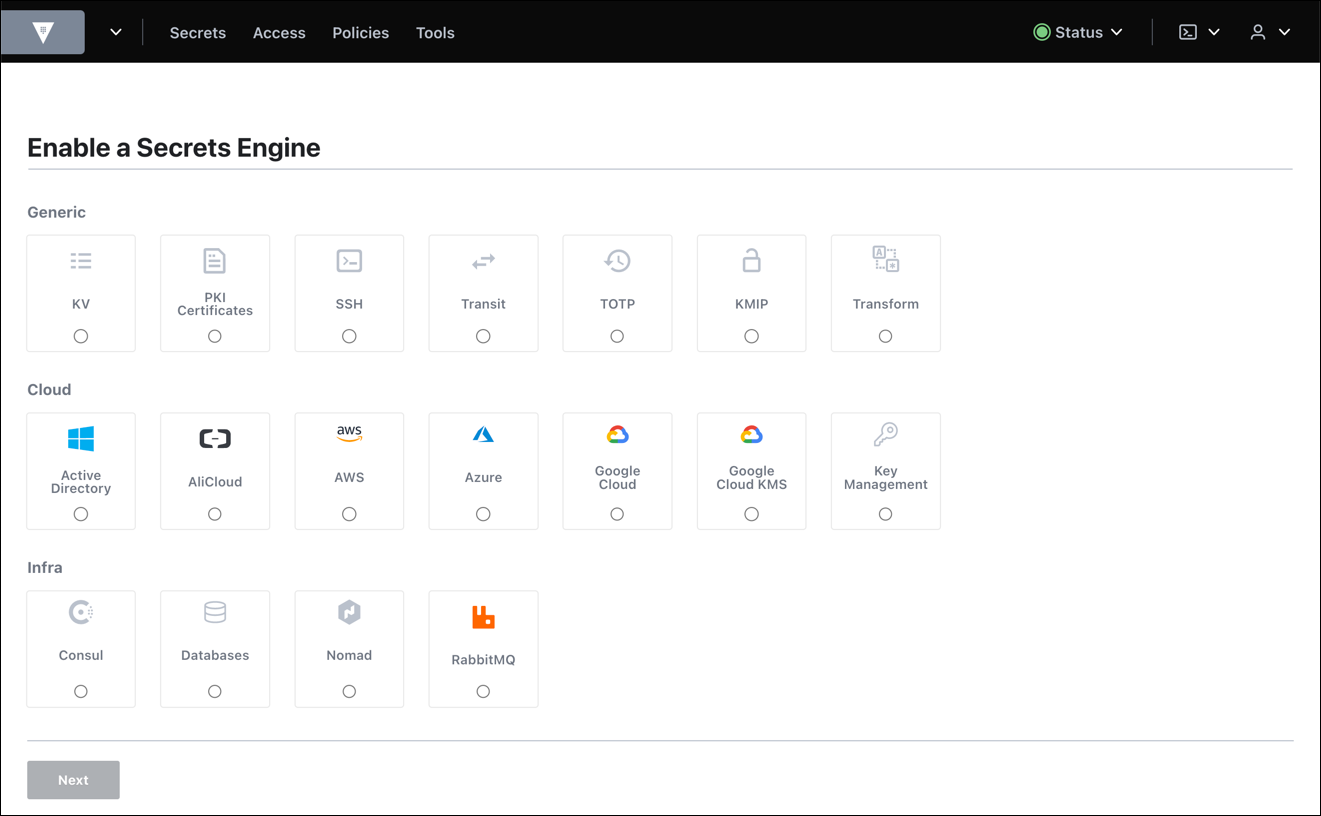
We leverage HashiCorp Vault capabilities for storing and managing our secrets and company passwords. HashiCorp Vault integrates with applications and tools to enable transparent secure sensitive information retrieval programmatically. By leveraging HashiCorp Vault we can go with IAC/CAC on almost everything we build. HashiCorp Vault also makes it easy to share secrets between team members and the organization.
Pros
- Store secrets
- Store configurations
- Integrate with kubernetes
- Audit log of changes
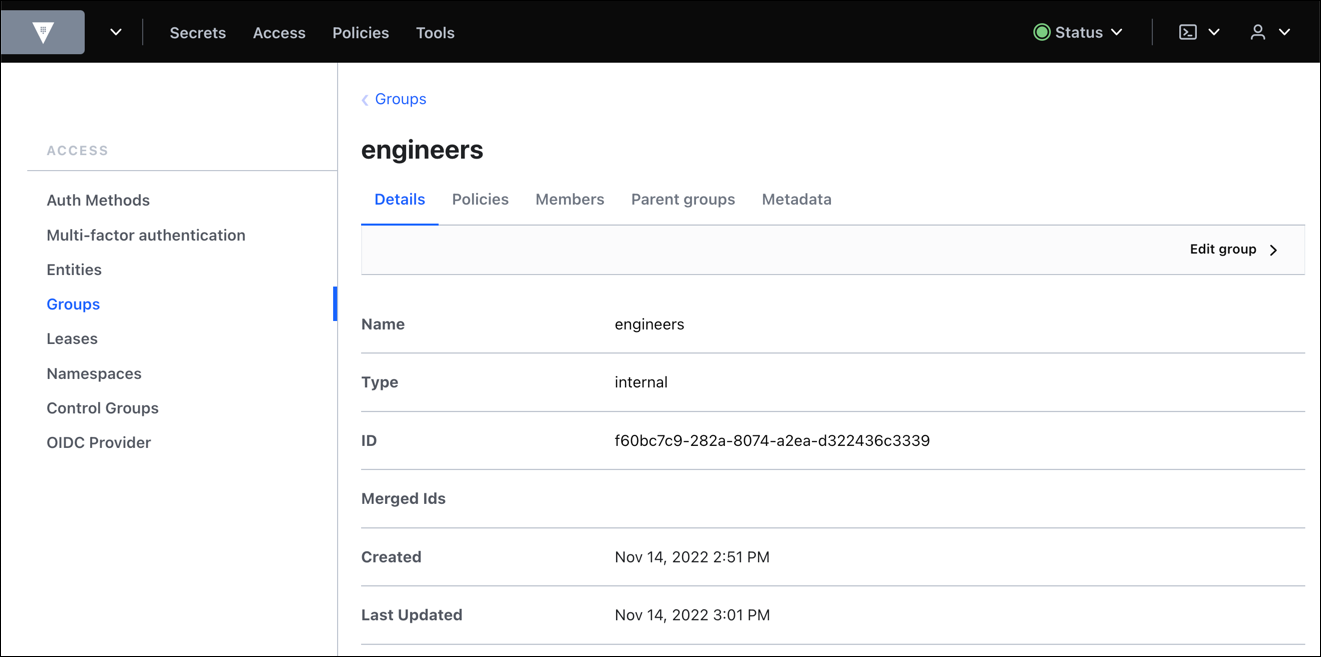
- Team secret sharing
- Real time in transit encryption
Cons
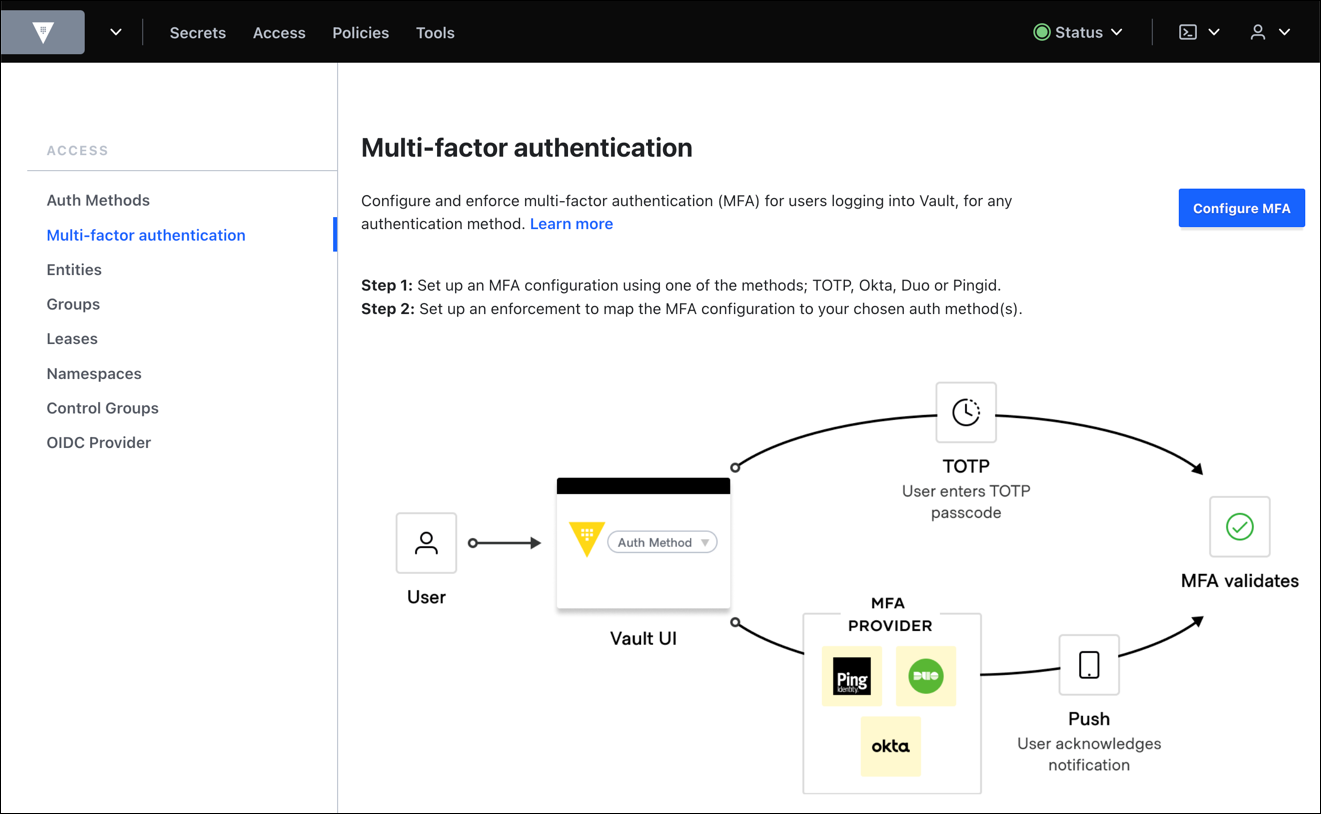
- Session Management is terrible to manage
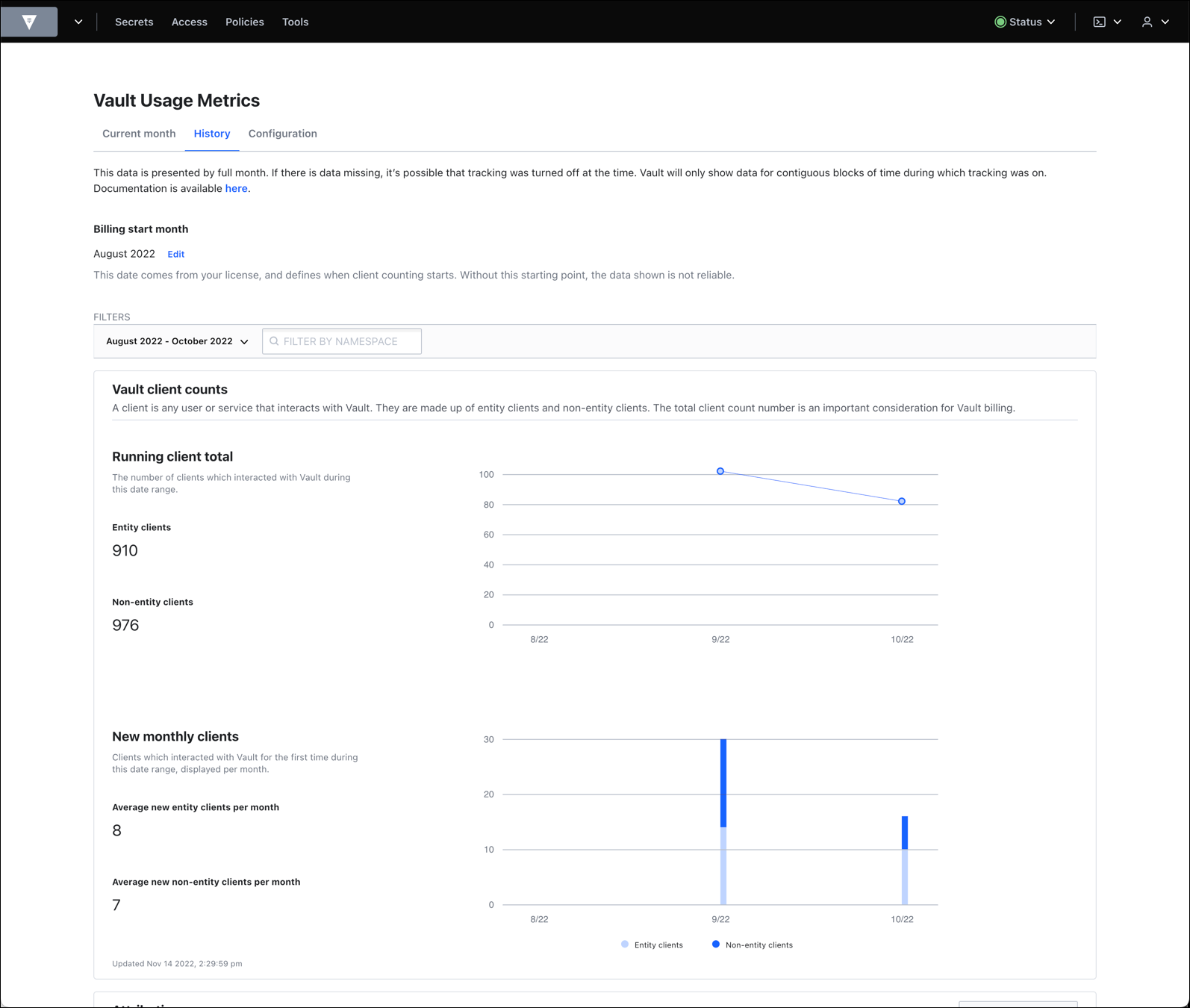
- Monitoring is hard and not enough information
- User management
- Configuration is too complex
- More user friendly UI
Return on Investment
- Vault enabled IAC for kubernetes applications
- Central configuration for applications
- Version Control on secrets
- Improved the company security and secret sharing experience
- Enabled the PCI compliance for the company
Alternatives Considered
Bitwarden and AWS Secrets Manager
Other Software Used
Cloudflare, Cloudflare Zero Trust Services, Amazon RDS Performance Insights, Amazon Kinesis, Amazon Simple Queue Service (SQS)