Open Bug Bounty vs. YesWeHack
Open Bug Bounty vs. YesWeHack
| Product | Rating | Most Used By | Product Summary | Starting Price |
|---|---|---|---|---|
Open Bug Bounty | N/A | Open Bug Bounty is an open, disintermediated, cost-free, and community-driven Bug Bounty platform for coordinated, responsible, and ISO 29147 compatible vulnerability disclosure. 862,692 coordinated disclosures, 488,651 fixed vulnerabilities,1285 bug bounties with 2,450 websites, 21,880 researchers, 1283 honor badges. Open Bug Bounty is used by Ebay, Berkeley University, Yamaha, IKEA, Verizon, Philips. | N/A | |
YesWeHack | N/A | YesWeHack is an Offensive Security and Exposure Management platform. It provides a suite of integrated, API-based solutions designed to secure organisations’ growing attack surfaces. The YesWeHack platform comprises: - Bug Bounty: Crowdsourced vulnerability discovery leveraging a global community of 135,000+ skilled ethical hackers through a platform-driven model. - Autonomous Pentest: Comprehensive asset discovery combined with ongoing exposure validation to… | N/A |
| Open Bug Bounty | YesWeHack | |||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Editions & Modules | No answers on this topic | No answers on this topic | ||||||||||||||
| Offerings |
| |||||||||||||||
| Entry-level Setup Fee | No setup fee | No setup fee | ||||||||||||||
| Additional Details | — | — | ||||||||||||||
| More Pricing Information | ||||||||||||||||
| Open Bug Bounty | YesWeHack | |
|---|---|---|
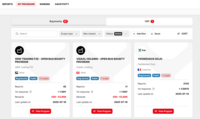
| ScreenShots | Open Bug Bounty Screenshots | YesWeHack Screenshots |