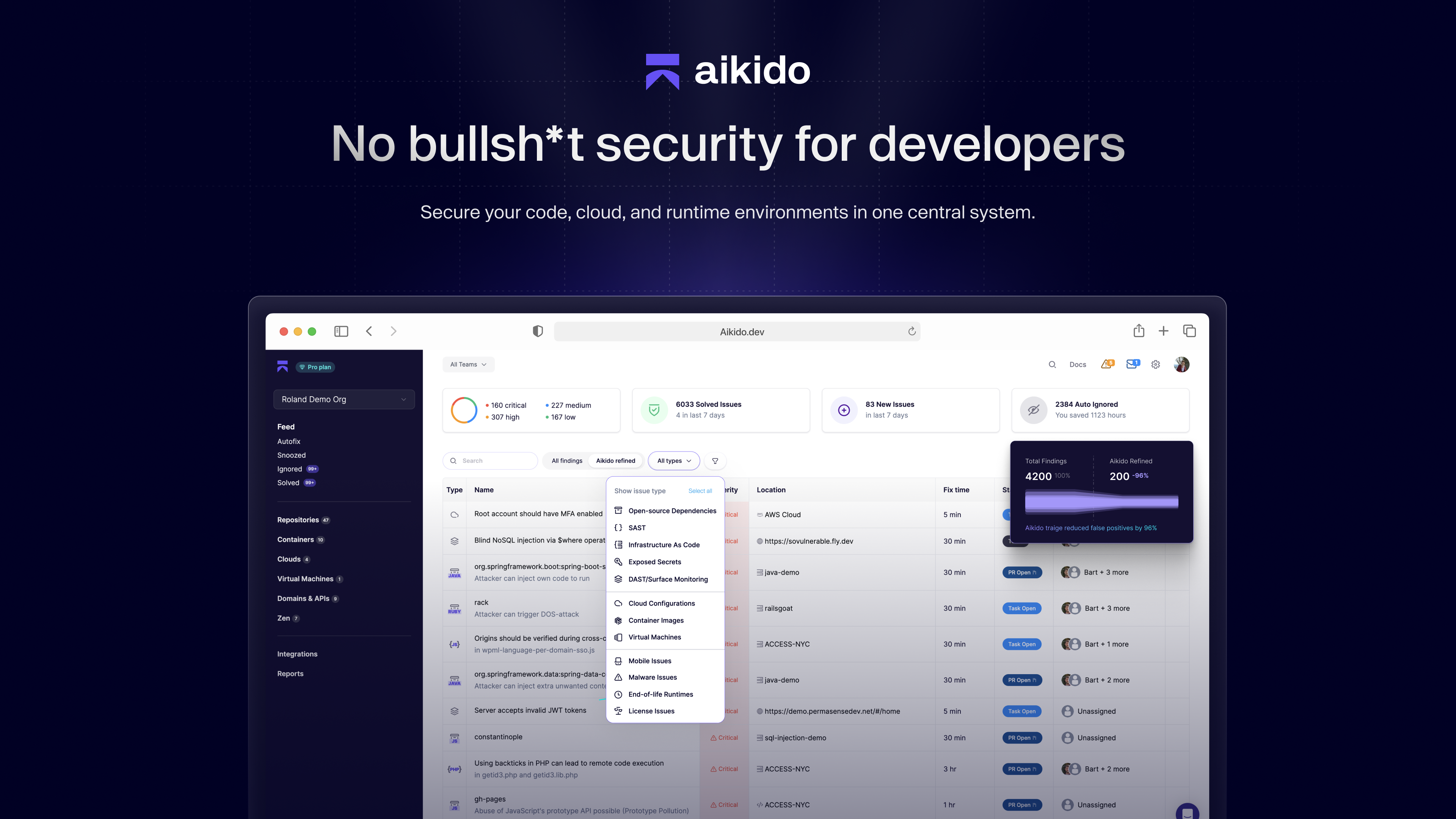
What is Aikido Security?
Aikido's security platform supports developers and security teams alike with full security visibility, insights, and automatic vulnerability fixes. Aikido helps security teams with:
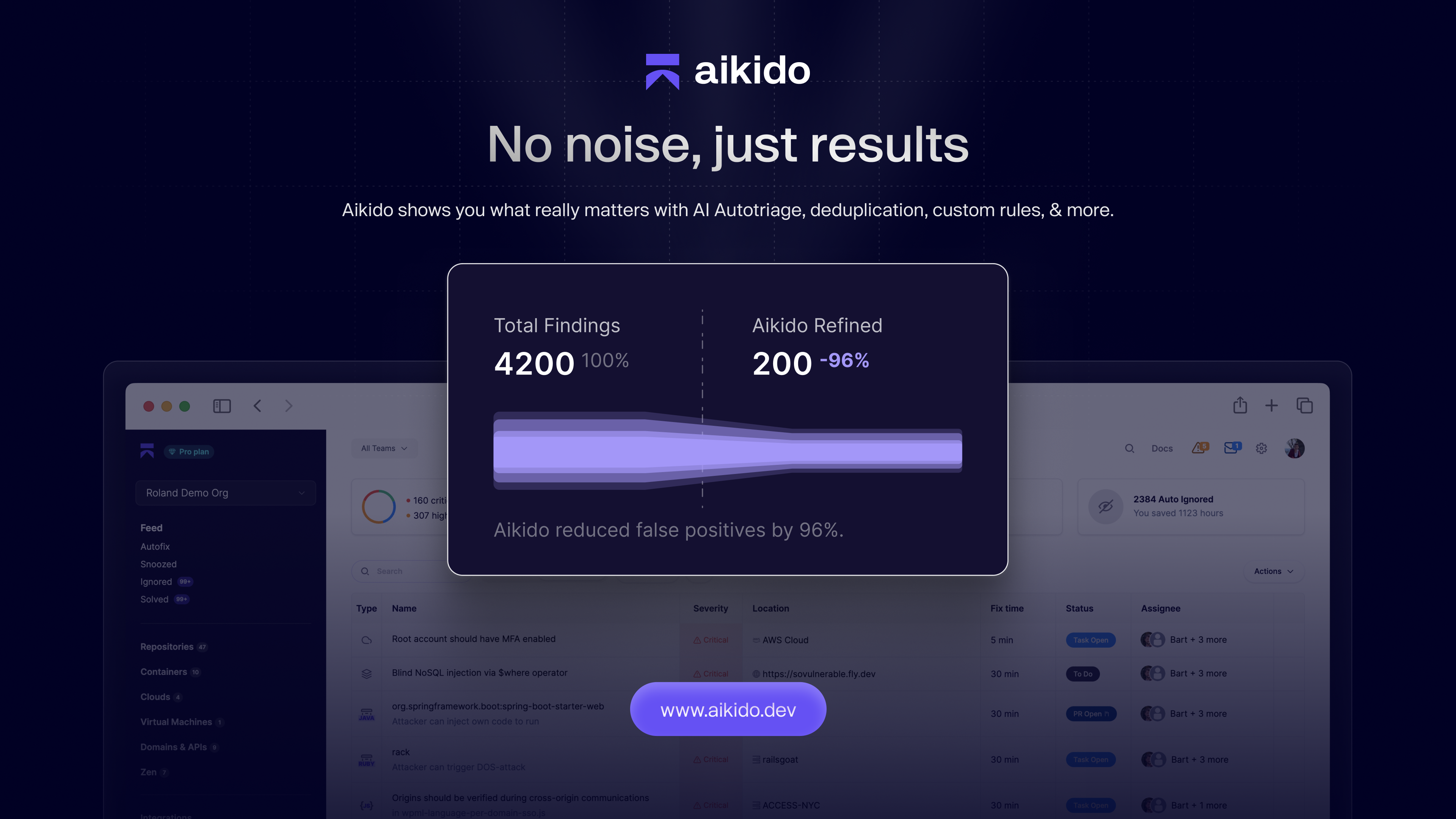
- False-positive reduction
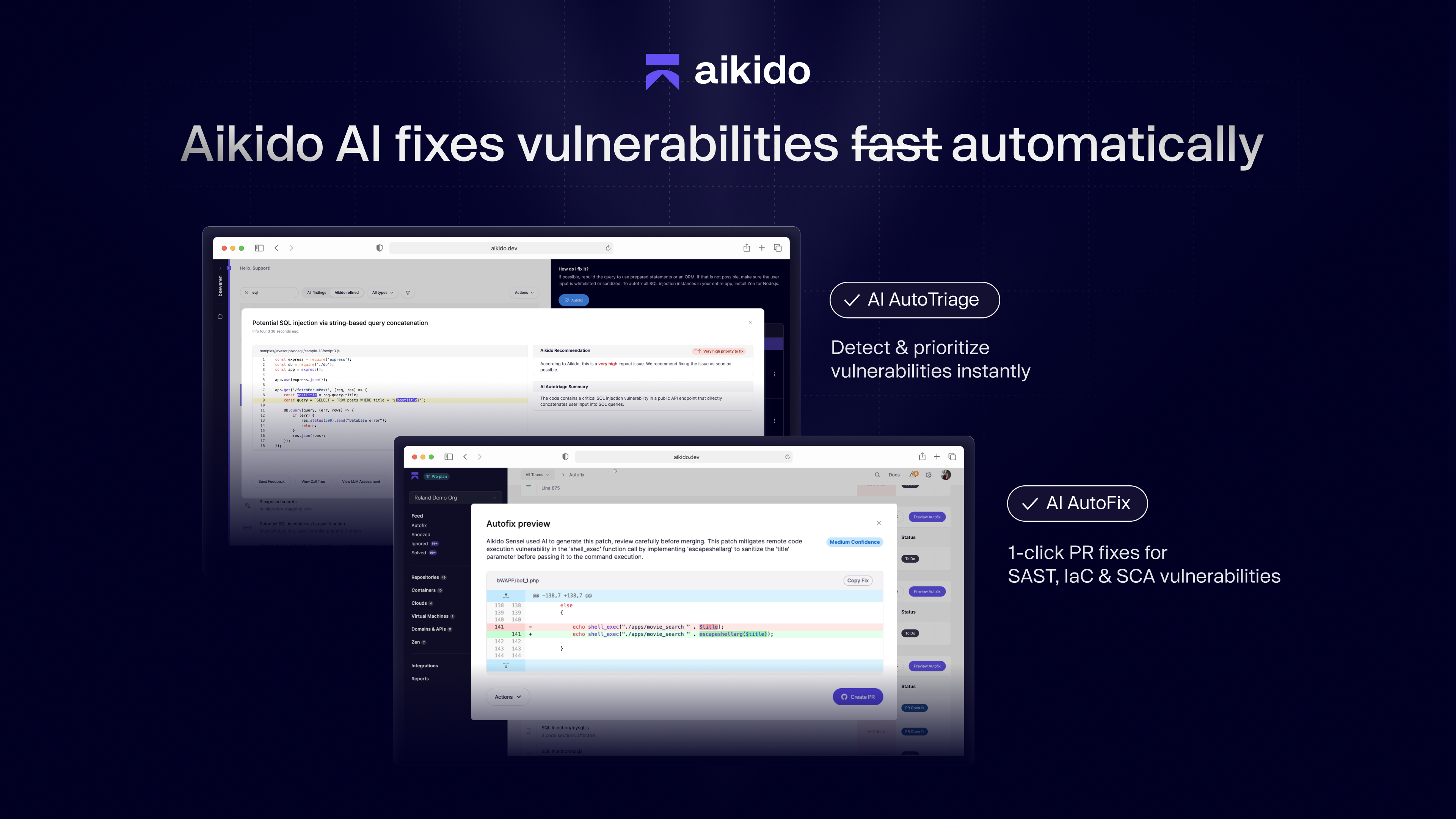
- AI Autotriage & AI Autofix
- Deep integration into the dev workflow (from IDEs and task managers to CI/CD gating)
- Automated Compliance
Aikido's covers the entire Software Development Lifecycle (SDLC), including: static application security testing (SAST), dynamic application security testing (DAST), infrastructure-as-code (IaC), container scanning, secrets detection, open source license scanning (SCA), cloud posture management (CSPM), and runtime protection.
Categories & Use Cases
Media
1 / 5
Top Performing Features
Vulnerability Intelligence
Software that is able to label and store information about vulnerabilities to access for future use cases.
Category average: 8.3
Threat Recognition
Detection and recognition of malicious software within a network that could pose a threat to sensitive information.
Category average: 7.9
Automated Alerts and Reporting
Systems in place to automatically alert, report, or notify of issues that may need timely remediation.
Category average: 8.2
Areas for Improvement
Web Scanning
Specifically scans webpages for potential threats or vulnerabilities.
Category average: 7.9
Vulnerability Classification
Prioritizing vulnerabilities, to determine which vulnerabilities are most urgent and require a quicker resolution.
Category average: 8.8
Threat Analysis
Analyzing known factors such as behavior patterns, affected areas, and other specific features to more easily identify a threat.
Category average: 7.8