A complete package / suite of tools to keep you secure on prem and online.
Use Cases and Deployment Scope
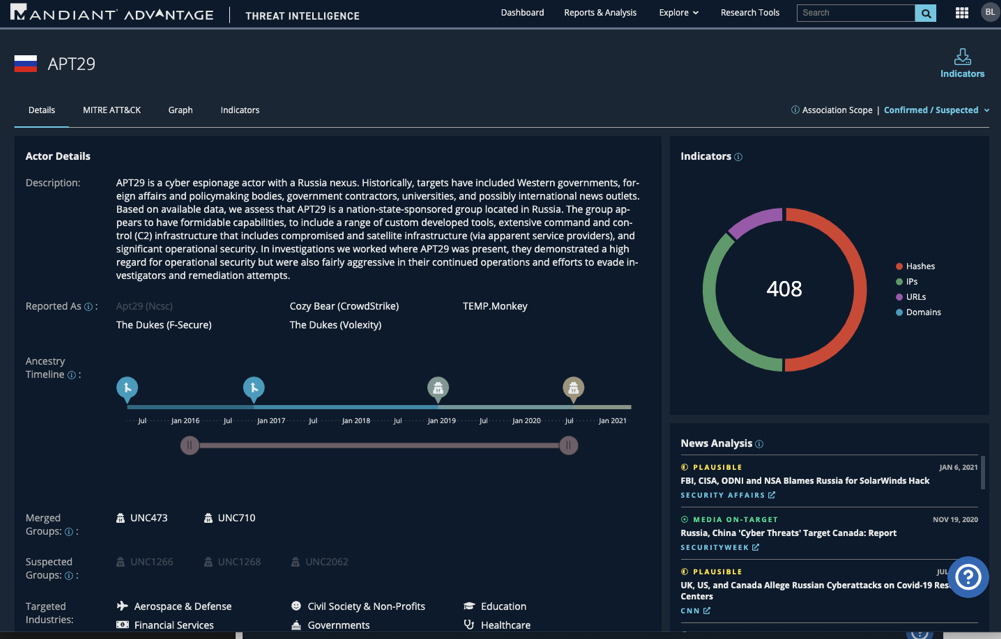
The deployment has been part of our managing service; this is part of the infrastructure service provided overall. It is used to monitor the behaviors of systems within the organization. The service allows us to spend time understanding various situations, occurrences, and patterns of threats and actors.
Pros
- Understanding a particular vulnerability within the software vendors we work with.
- Understanding the threat pattern and occurrences.
- Understanding bad actor behaviors and expert information from the service itself.
Cons
- Most cases are usually up to date, but there have been instances where we had to provide additional information or proactive findings.
- The support responses to noncritical cases are a bit slow.
Return on Investment
- With the tool, we have been able to avoid and learn early on certain threats that were exposed.
- We have been able to provide up-to-date reports to our internal management with clear and concise information.
Alternatives Considered
Broadcom Symantec Email Threat Detection and Response
Usability
Other Software Used
Broadcom Symantec Email Threat Detection and Response, McAfee DLP Endpoint, Atlassian Crowd