HackerOne vs. Intigriti vs. YesWeHack
HackerOne vs. Intigriti vs. YesWeHack
| Product | Rating | Most Used By | Product Summary | Starting Price |
|---|---|---|---|---|
HackerOne | N/A | HackerOne is a hacker-powered security platform, helping organizations find and fix critical vulnerabilities before they can be exploited, from the company of the same name in San Francisco. The service is used for vulnerability location, pen testing, bug bounty, and vulnerability triage services. | N/A | |
Intigriti | N/A | Intigriti is an ethical hacking and bug bounty platform oprating primarily in the European Union, allowing users to carry out research and conduct security evaluations. | N/A | |
YesWeHack | N/A | YesWeHack is an Offensive Security and Exposure Management platform. It provides a suite of integrated, API-based solutions designed to secure organisations’ growing attack surfaces. The YesWeHack platform comprises: - Bug Bounty: Crowdsourced vulnerability discovery leveraging a global community of 135,000+ skilled ethical hackers through a platform-driven model. - Autonomous Pentest: Comprehensive asset discovery combined with ongoing exposure validation to… | N/A |
| HackerOne | Intigriti | YesWeHack | ||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| Editions & Modules | No answers on this topic | No answers on this topic | No answers on this topic | |||||||||||||||||||||
| Offerings |
| |||||||||||||||||||||||
| Entry-level Setup Fee | No setup fee | Optional | No setup fee | |||||||||||||||||||||
| Additional Details | For more information please email www.hackerone.com/contact or find us on the AWS Marketplace: https://aws.amazon.com/marketplace/seller-profile?id=10857e7c-011b-476d-b938-b587deba31cf | — | — | |||||||||||||||||||||
| More Pricing Information | ||||||||||||||||||||||||
| HackerOne | Intigriti | YesWeHack |
|---|
| HackerOne | Intigriti | YesWeHack | |
|---|---|---|---|
| Likelihood to Recommend | 7.0 (2 ratings) | - (0 ratings) | - (0 ratings) |
| HackerOne | Intigriti | YesWeHack | |
|---|---|---|---|
| Likelihood to Recommend |  HackerOne
| Intigriti No answers on this topic | YesWeHack No answers on this topic |
| Pros |  HackerOne
| Intigriti No answers on this topic | YesWeHack No answers on this topic |
| Cons |  HackerOne
| Intigriti No answers on this topic | YesWeHack No answers on this topic |
| Alternatives Considered |  HackerOne
| Intigriti No answers on this topic | YesWeHack No answers on this topic |
| Return on Investment |  HackerOne
| Intigriti No answers on this topic | YesWeHack No answers on this topic |
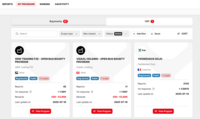
| ScreenShots | YesWeHack Screenshots |