What is Hut Six Security?
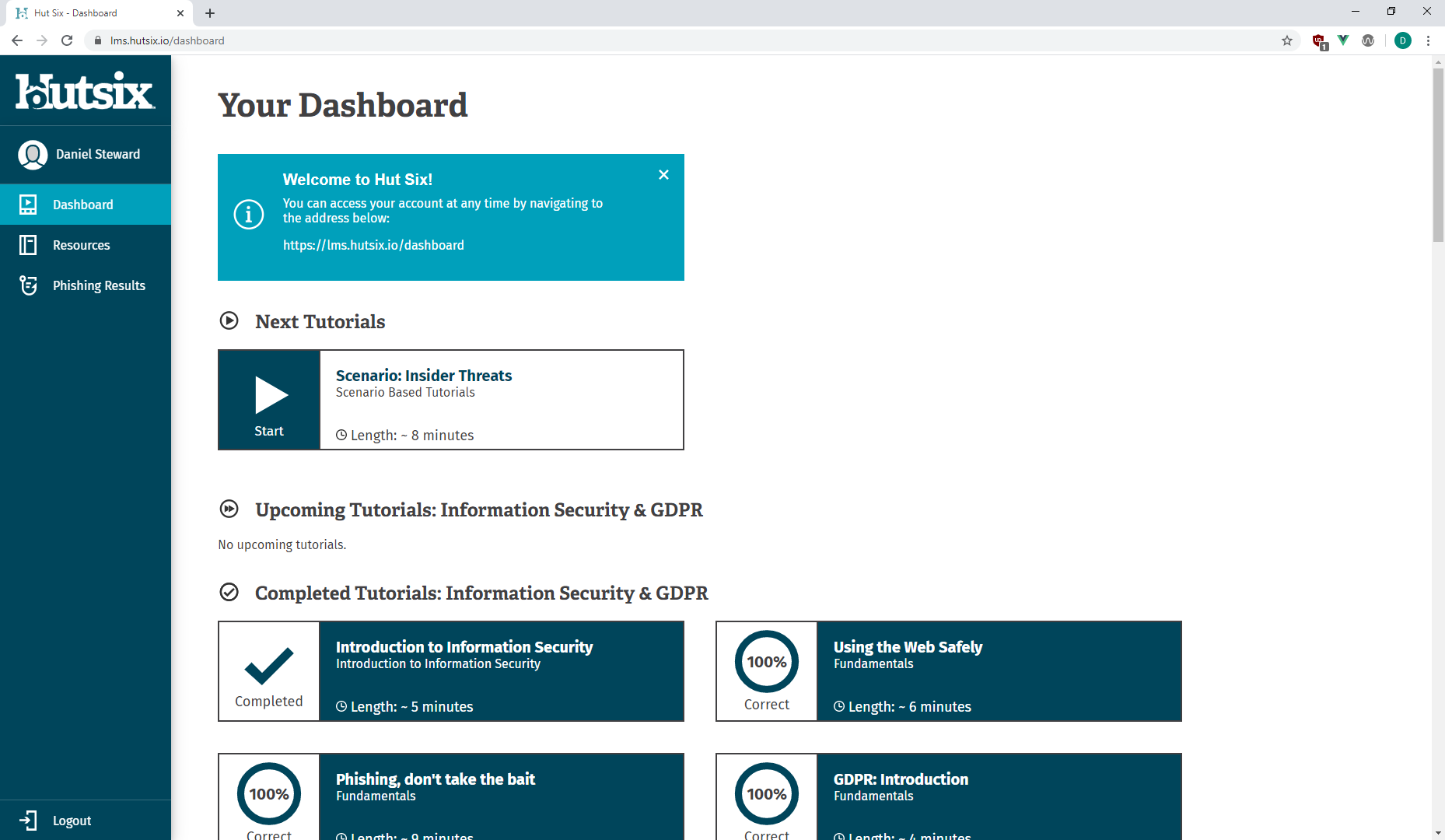
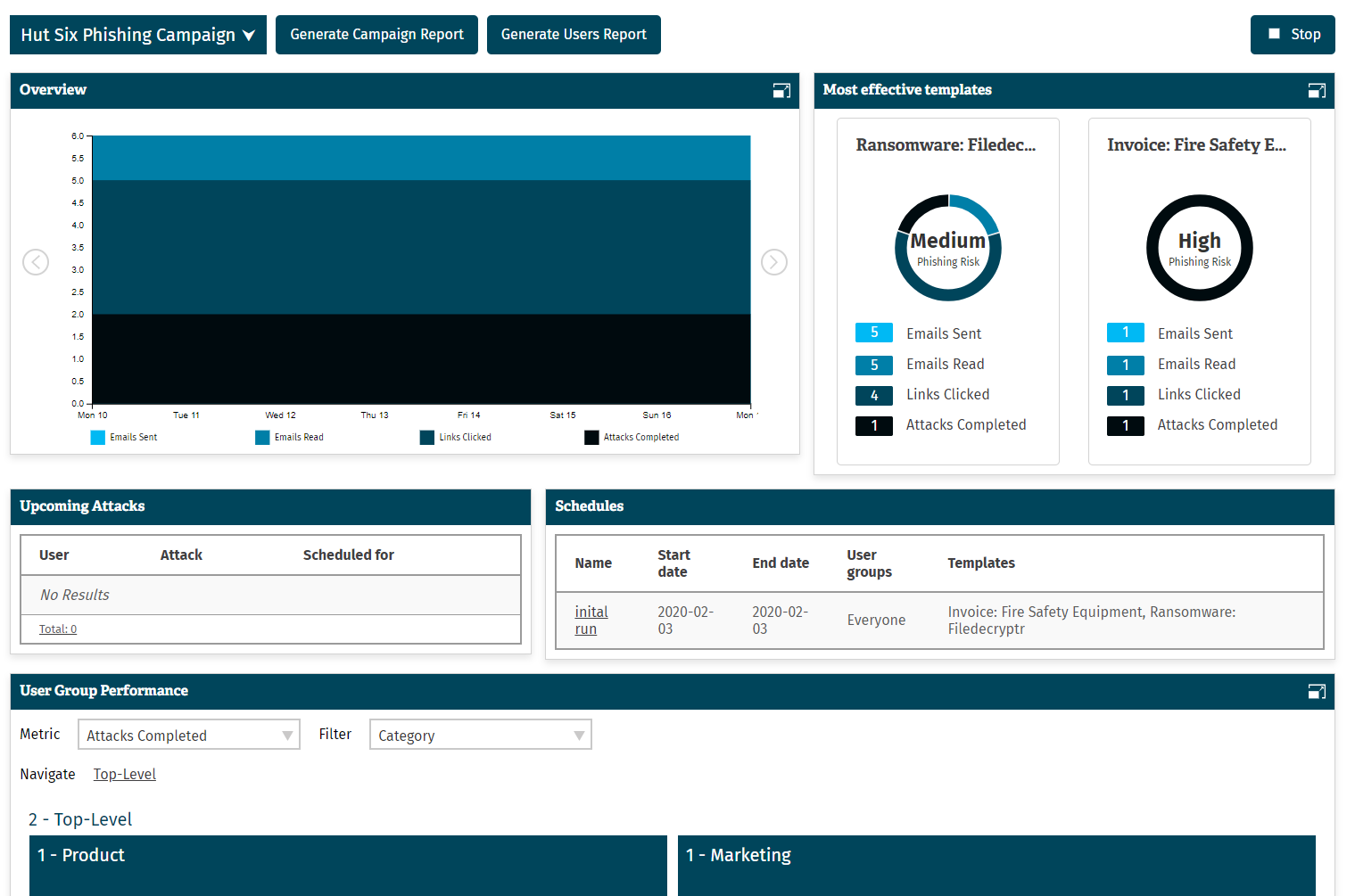
Hut Six Security allows users to train, test and track an organisation's information security culture with one comprehensive solution. The service combines Hut Six's Information Security Awareness Training with its Simulated Phishing platform. The dashboard integrates training results with phishing metrics to give real-world validation of the organisation's human cyber risk.
Features
- Comprehensive security awareness course with animated and voiced tutorials
- Phishing Simulation, automated campaigns and configurable email templates
- Add custom questions to assess your workforce
- Real-time reporting dashboards
- Automated notifications and alerts
- Single Sign On and Active Directory Integrations
- Learning Management System, built in-house, designed for information security training
- Mobile compatible
- Subtitles, high contrast and screen reader compliant
- Integrate into existing Learning Management Systems
Benefits
- Assess your staff against the latest phishing threats
- Change user behaviour through increased information security awareness
- Demonstrate understanding of security policies through custom questions
- Meet compliance obligations such as ISO27001, Cyber Essentials, GDPR
- Simplify the security audit process with easily readable training metrics
- Measure the information security risk to your organisation
- Target at-risk users with additional refresher modules
- Regular and concise training maintains awareness in your organisation
- Manage your awareness and phishing campaigns in one dashboard
Categories & Use Cases
Media
1 / 4