What is Infocyte HUNT?
Infocyte HUNT aims to provide an easy-to-use, yet powerful enterprise endpoint security solution.
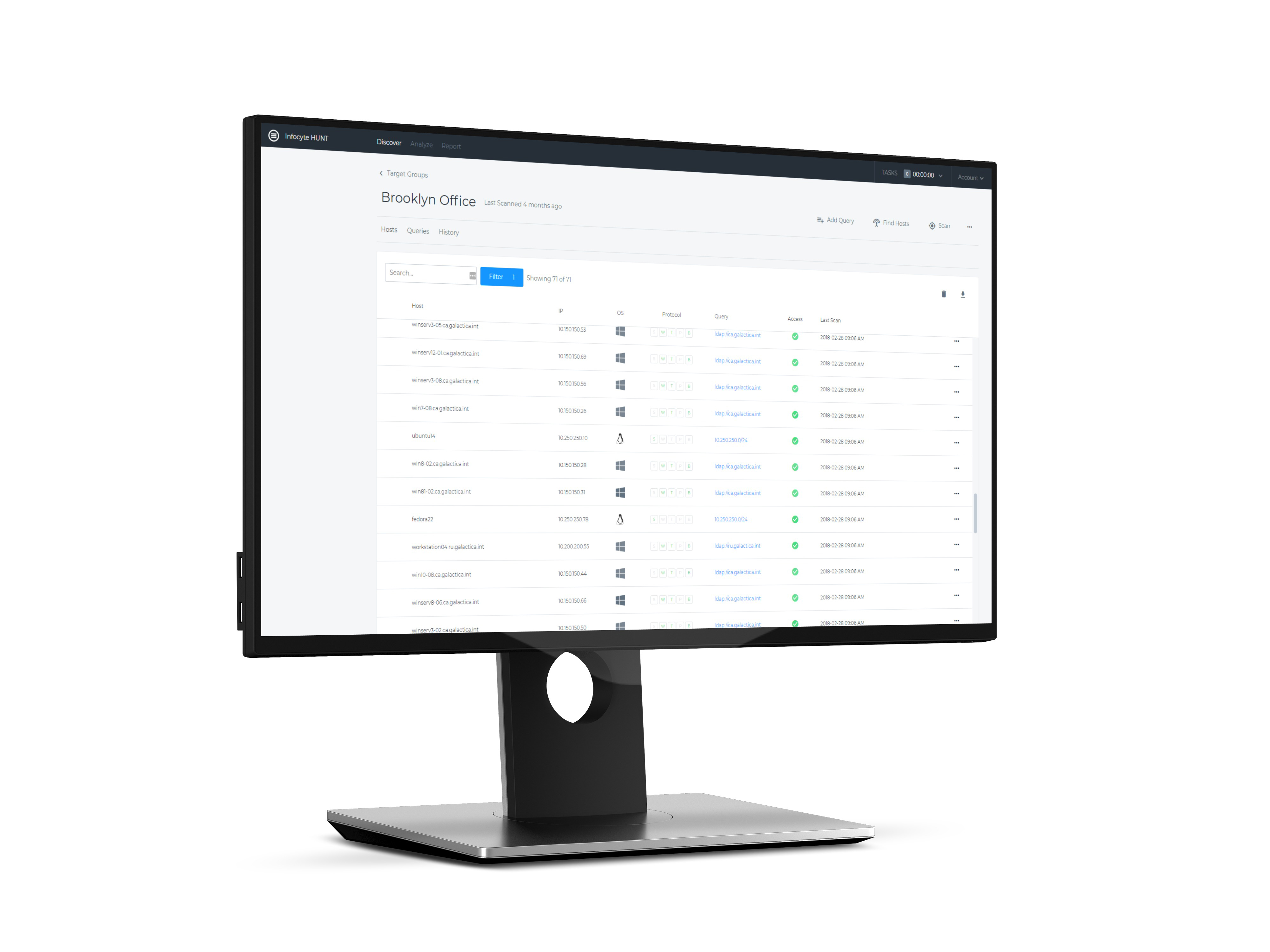
Infocyte HUNT is a threat hunting software/platform designed to limit risk and eliminate dwell time by enabling an organization’s own IT and security professionals to proactively discover malware and persistent threats, active or dormant, that have successfully breached existing defenses.
According to the vendor, Infocyte HUNT uses a forensic methodology that is different from other threat hunting solutions. Other threat hunting tools rely on analyzing event based security logs from cumbersome sensors and software installed on the endpoint. Rather than analyzing security/event logs, Infocyte directly inspects live volatile memory in the host in order to gather primary data including rootkit hooks, malware persistence mechanisms, application vulnerabilities, and other digital forensics artifacts.
By deploying lightweight dissolvable agents, HUNT sweeps thousands of endpoints per hour. This sweep gathers forensic data from each host, even those without conventional detection tools installed. The collected forensic data, when combined with Infocyte's analysis automation, provides a more comprehensive picture of the state of your endpoints.
Infocyte says their approach is unique, and they call it Forensic State Analysis (FSA).
Categories & Use Cases
Media
1 / 3