Power up Your Productivity with Pentest-Tools.com
Use Cases and Deployment Scope
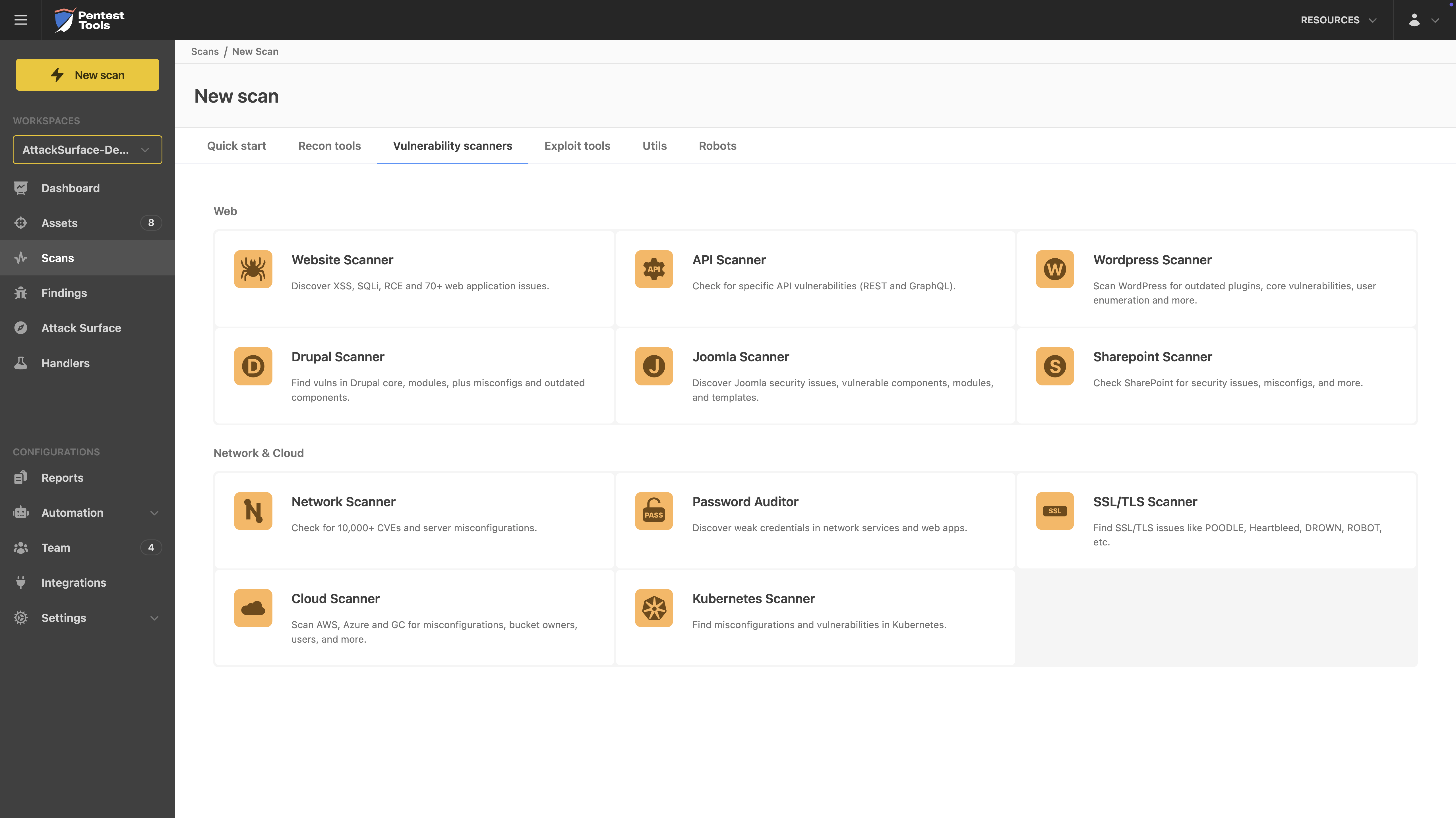
Pentest-Tools.com is a website
that provides a range of online tools and services for pentesting, or ethical
hacking. These tools are designed to help identify and address vulnerabilities
in computer systems and networks.
In
our organization, Pentest-Tools.com is used to assess the security of the
company's systems and identify potential weaknesses that could be exploited by
malicious hackers. This helps us protect our assets and sensitive information
from cyber attacks, and also helps ensure compliance with relevant regulations
and standards. In particular, we like to utilise this product for it's website/port scanners, and it's password auditor, since these allow us to set up automated alerts when something has gone awry, giving us situational awareness at all times.
Pros
- Cheaper than some other platforms
- Good support
- Cloud based
- Integrates well with identity providers
Cons
- No logging for things like scanning. This means you don't actually know when the scan has failed if you're not immediately on the ball.
- Reports could look better. It would be good to be able to customise the report with some different styles to suit your company's branding.
- Could have better tutorials.
- It may be useful to have a feature similar to Microsoft Secure Score, which compares your organisation to similar ones, so that you have a reference of how secure your environment actually is.
Most Important Features
- Attack surface view allows you to see the multiple different scanners in one place, giving you an overview of that targets complete security picture.
- Cloud based. This is really important because tools like this need to be easily accessible for ease of use. Ideally you don't want to have to access a dedicated device every time you want to run a report, because it can be a real pain to do so whilst you are on the go.
- Quick and easy to generate reports. This was useful to sell internally when we wanted to purchase the tool, and I imagine it would be useful for MSSP's as well, as the ability to quickly spin up a report for exactly what you need immediately is an impressive thing to do. You can edit the report before generating it so that it suits your needs, only including the information that is relevant.
- White label features for the reporting
Return on Investment
- Price point allows us to sell the solution at an excellent margin
- Freed up time due to the automated solutions, allowing us to utilise staff better
- Use from anywhere due to being cloud based
Alternatives Considered
Microsoft Sentinel, Microsoft Defender for Endpoint, Metasploit, Nmap, Kali Linux and Wireshark
Other Software Used
Microsoft Defender for Endpoint, Trend Micro Apex One, Cisco Umbrella, Malwarebytes Endpoint Protection, Cisco Packet Tracer (part of Cisco Networking Academy)