What is Syteca?
Syteca is a privileged access management platform with built-in ITDR used to control privileged access and detect identity threats.
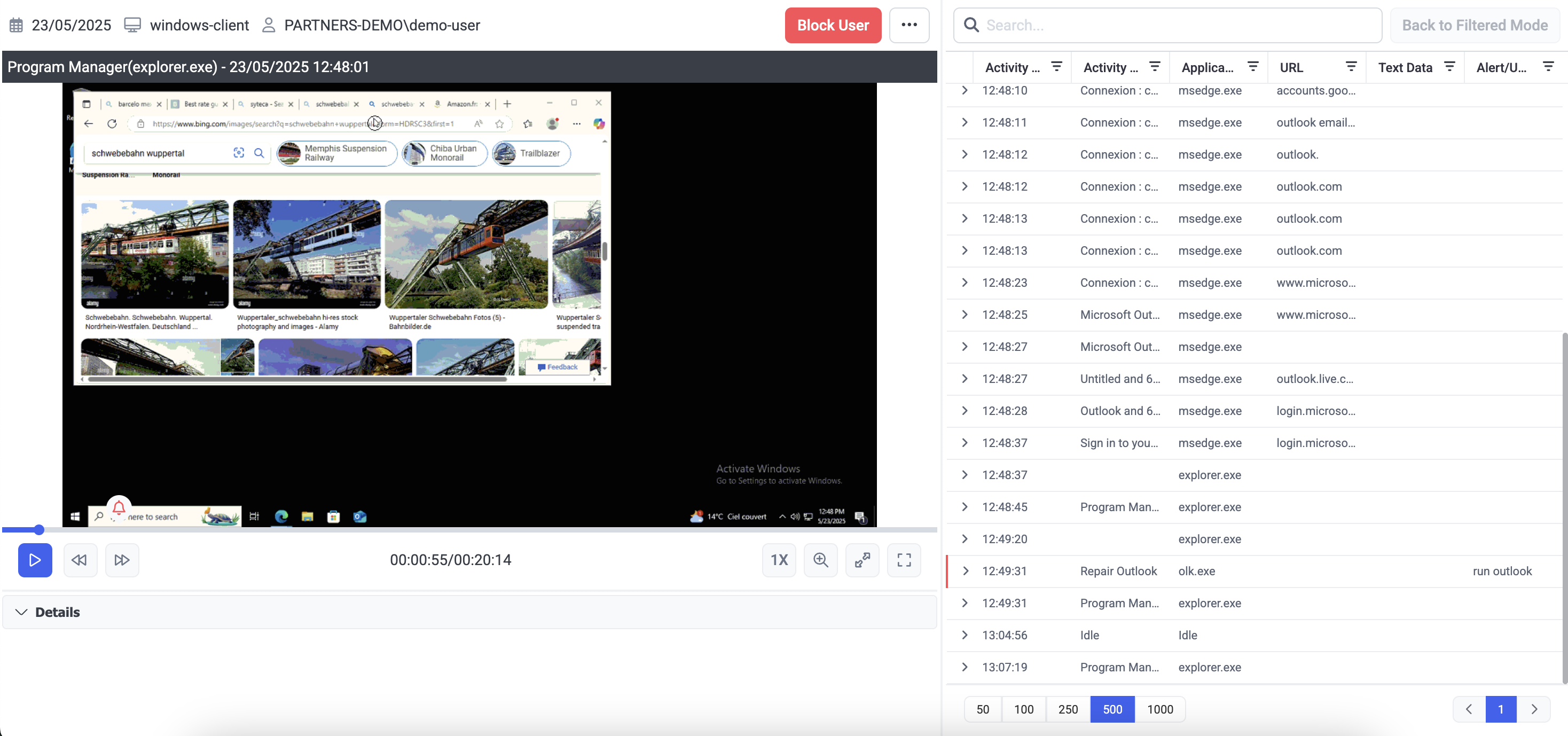
Syteca unifies privileged access control with full session visibility and built-in ITDR. It gives security teams the clarity, evidence, and control needed to understand what happens after access is granted and to address identity-driven risks that traditional PAM cannot see.
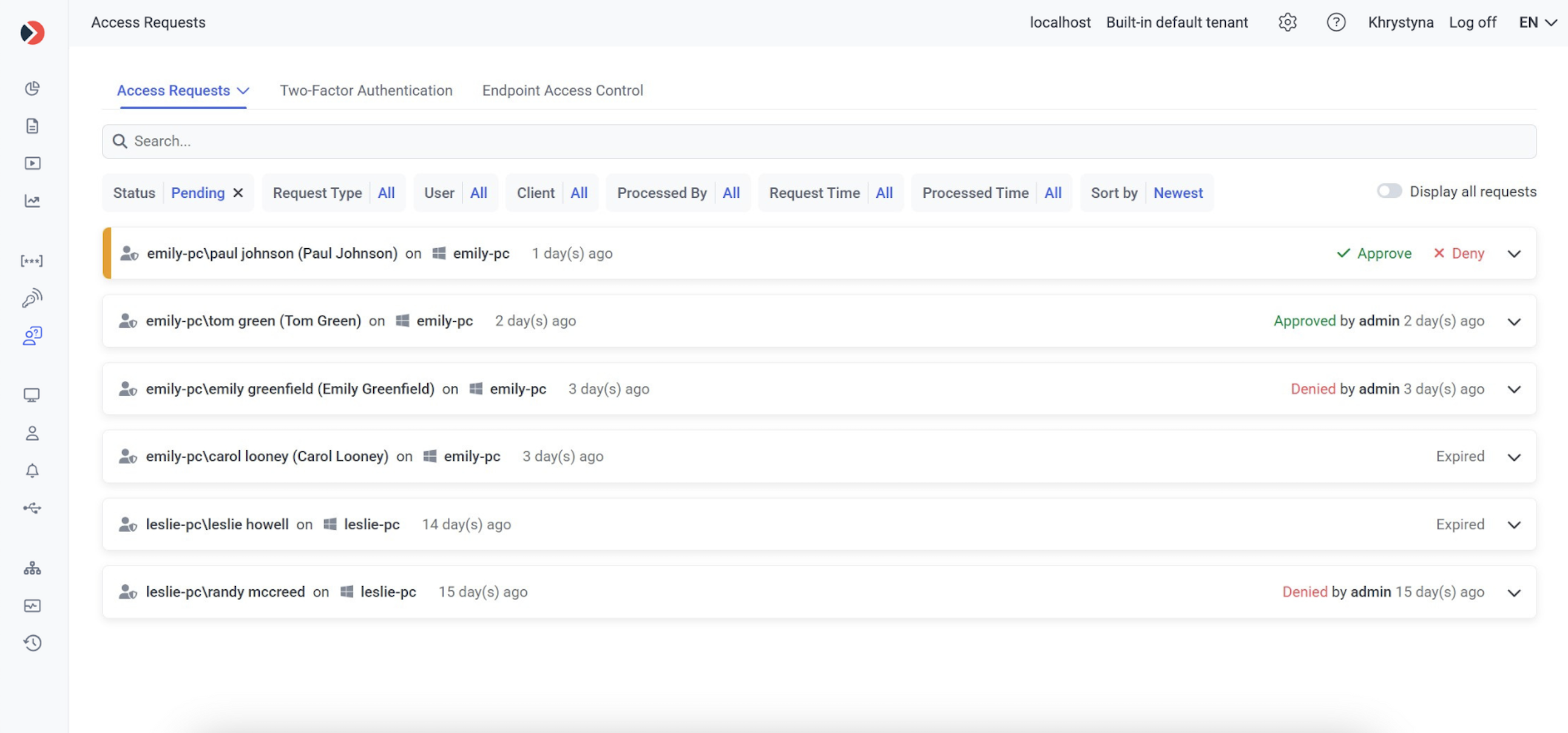
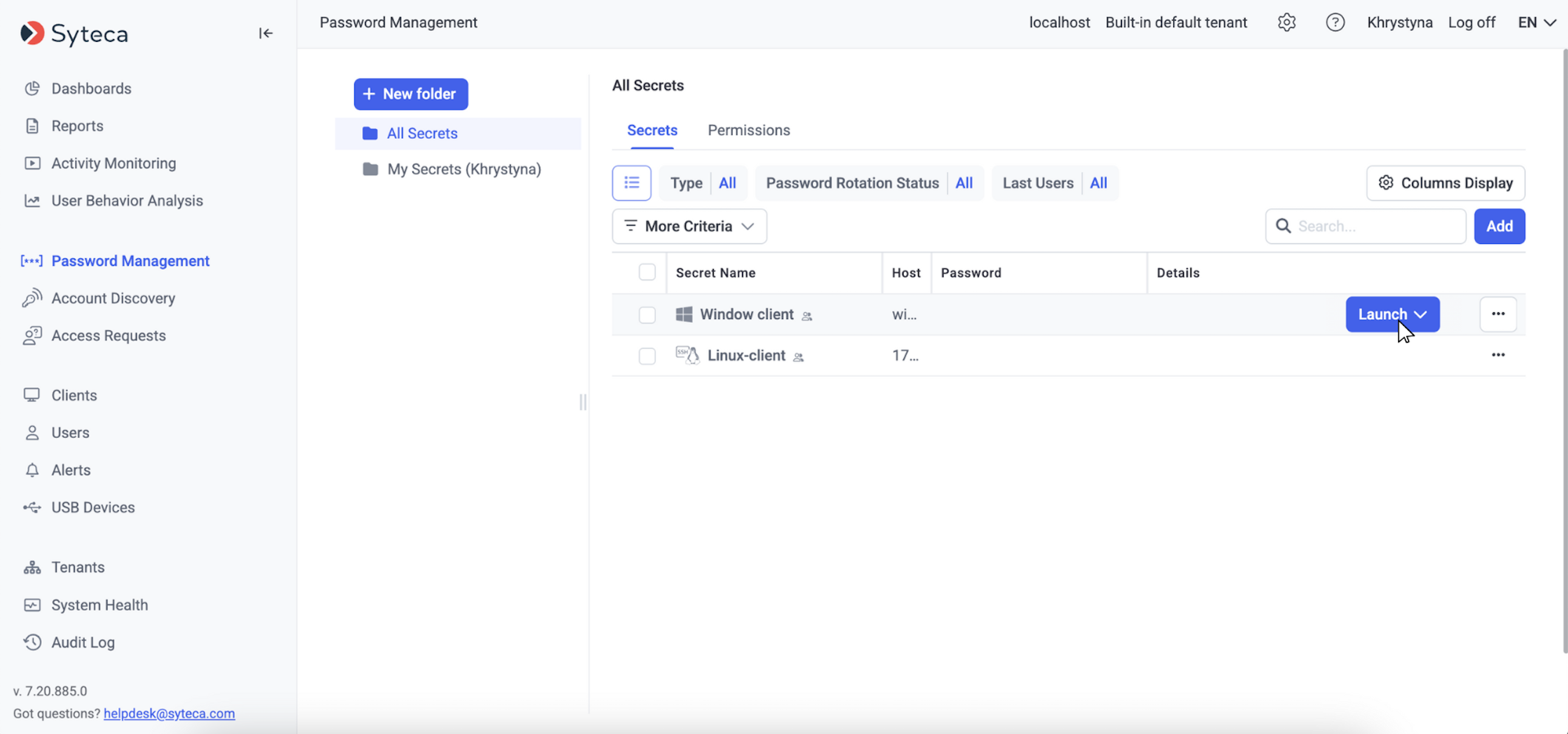
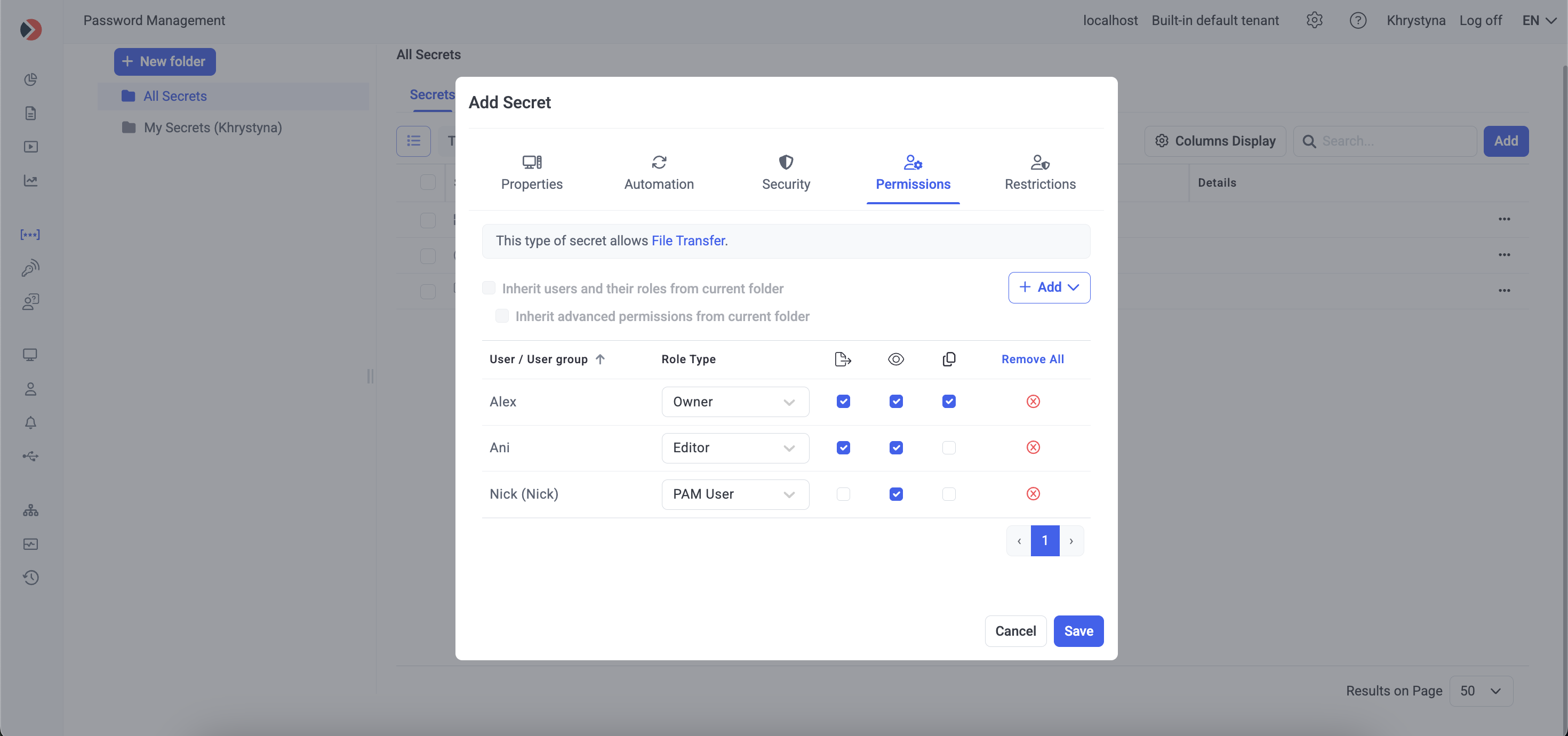
Syteca combines the essential capabilities of modern PAM — automated account discovery, privileged access control, credential and password management, identity verification, and just-in-time access — with forensic-grade session visibility and ITDR insights. According to the vendor, this enables security teams to understand what happens after access is granted, close critical visibility gaps, and address access-based risks that legacy PAM solutions cannot detect.
Syteca is specifically designed to secure organizations against threats caused by insiders. Platform works across Windows, macOS, and Linux, and supports on-premises, cloud, and hybrid deployments. Licensing is modular — the user selects and pays only for the capabilities needed.
Key Benefits:
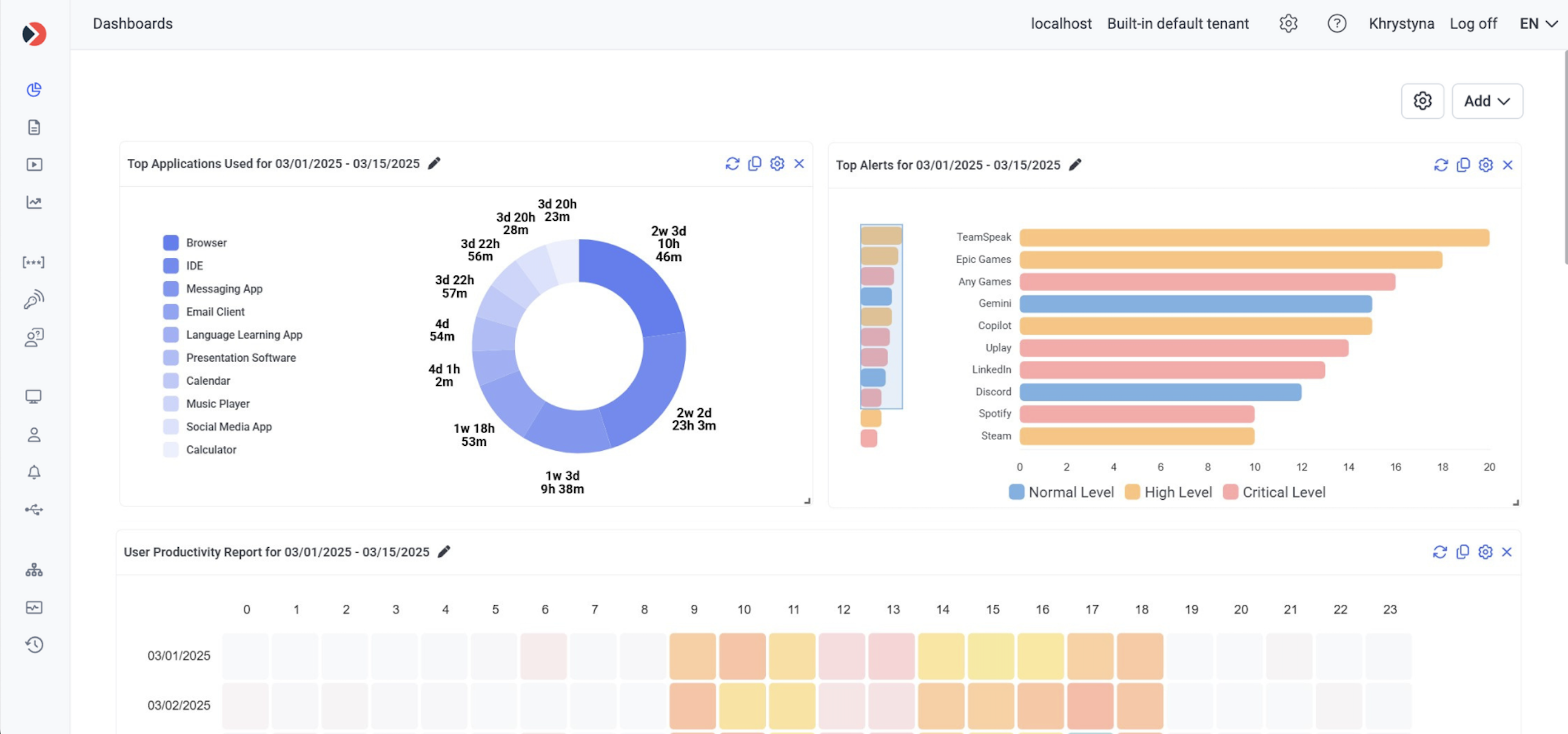
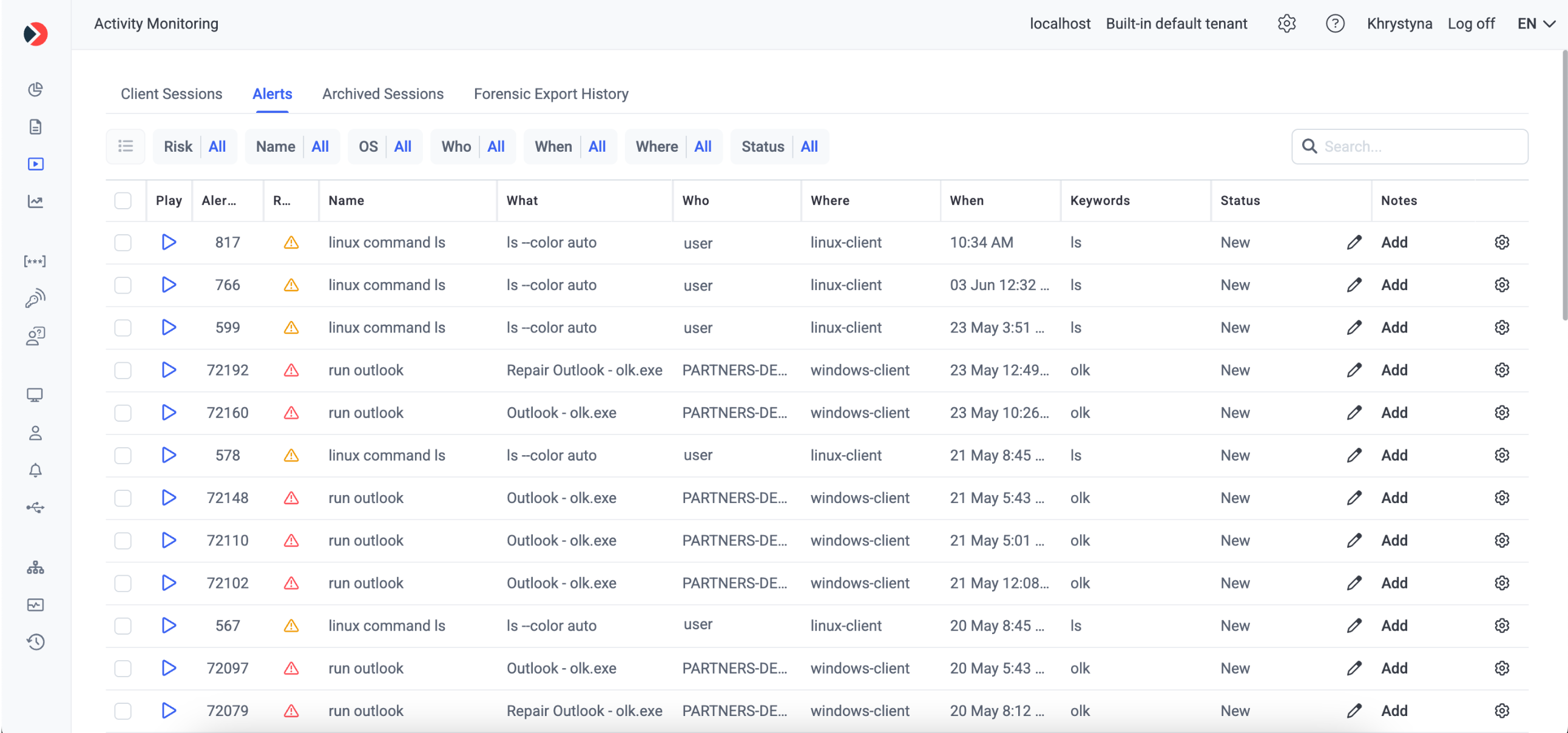
- Visibility: complete clarity into privileged sessions with forensic-level UAM and full activity recordings.
- Control: secure privileged access with modern, granular PAM and built-in ITDR safeguards.
- Efficiency: streamlined access security with a lightweight platform that deploys fast, scales, and reduces operational overhead.
- Confidence: transparent sessions, clear evidence, and trusted ITDR insights to inform security decisions.
Categories & Use Cases
Media
1 / 6