Best Deal!
Use Cases and Deployment Scope
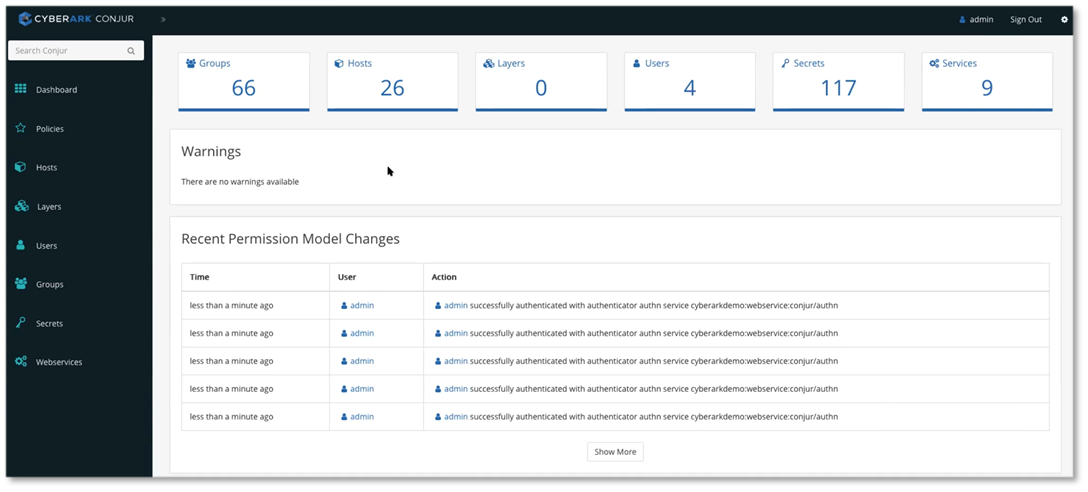
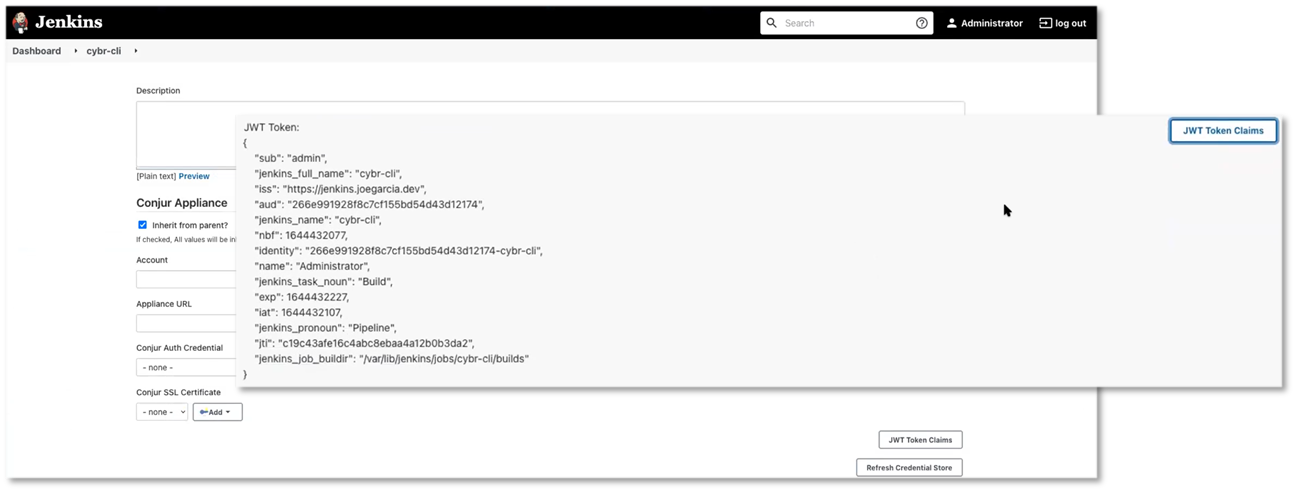
The Cyberark Conjur tool helped my organization to secure and manage secrets such as passwords, keys, and certificates. It acts as a central repository for storing and managing sensitive information, as well as tools for controlling access to those secrets based on role-based access control.
Pros
- Secret Management : Allows organizations to securely store, manage and rotate sensitive data and secrets, such as passwords and API keys
Cons
- Mobile Support : Cyberark Conjur doesn't have mobile app and it is not optimised for those devices.
Most Important Features
- Multi Cloud Support : Conjur Support for multiple cloud environments is important, as it allows users to protect their sensitive data and systems regardless of where they are hosted
Return on Investment
- Conjur has the potential to have a positive impact on a business's overall security objectives by providing roubust secure control, secrets management, and compliance capabilities. This helped to prevent from data breaches, ensured compliance with industry regulations, and improved overall security posture