Use Cases and Deployment Scope
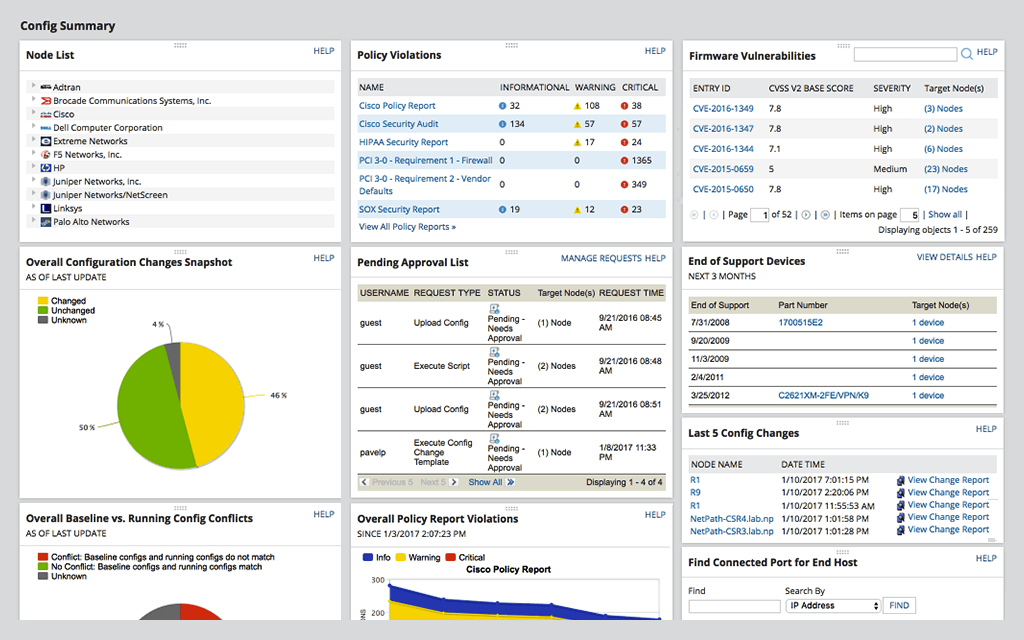
Our organization uses SolarWinds Network Configuration Manager (NCM) to take over configuration management duties and responsibilities for the networking systems, assets, and devices within our IT environment. Besides that, SolarWinds Network Configuration Manager (NCM) is being utilized within our organization for its configuration backup and restore capabilities. Also, NCM has the ability to conduct compliance reporting and vulnerability assessment of network resources.